Unearthing academic fraud has become a complex challenge in the digital age. Institutions are increasingly relying on responsible hackers to uncover instances of cheating through sophisticated techniques. These skilled professionals infiltrate systems, mimicking the actions of malicious actors to pinpoint vulnerabilities exploited by cheaters.
- Their investigations often involve reviewing student network traffic for suspicious activity, such as data transfer during exams.
- Moreover, they may implement hidden applications to observe students' computer behavior for signs of cheating.
- Ultimately, ethical hacking provides institutions with valuable insights into the evolving methods used by cheaters, enabling them to develop more effective countermeasures.
Detecting Dishonesty: Mobile Tracking & Online Evidence Analysis
In today's virtual landscape, uncovering fraud has become increasingly challenging. Exposing the truth often requires specialized tools and techniques that delve into the immense amount of data generated by our integrated lives. Phone monitoring and social media forensics have emerged as powerful weapons in this battle against misinformation. Through meticulous analysis of call logs, text messages, and social footprints, investigators can expose hidden patterns and connections that shed light on suspicious activities.
- Sophisticated phone monitoring software can capture a wide range of data, including call duration, contact information, GPS location, and even logged voice messages.
- Digital footprint analysis involves examining publicly available information on platforms like Facebook, Twitter, and Instagram to construct a comprehensive picture of an individual's online behavior and interactions.
Finally, phone monitoring and social media forensics play a crucial role in legal proceedings. They provide valuable insights that can help confirm information, identify potential threats, and achieve justice.
Cyber Security Audit : Detect and Prevent Data Breaches
In today's dynamic digital landscape, safeguarding sensitive data has become paramount. A comprehensive security assessment is crucial for organizations of all sizes to identify vulnerabilities and implement robust measures to prevent data breaches. By proactively assessing their systems, organizations can harden their defenses against malicious actors and protect themselves from the devastating consequences of a data breach.
- Scheduled reviews enable organizations to assess the effectiveness of existing security controls.
- Penetration testing helps identify weaknesses in systems and applications before they can be exploited.
- Enforcing strong passwords adds an extra layer of security to user accounts.
A well-planned cybersecurity audit provides invaluable insights into an organization's security posture, allowing for proactive improvements to mitigate threats and protect sensitive data.
Social Media Investigation
The digital realm has become a remote access hack breeding ground for malicious actors, who exploit social media platforms to scam unsuspecting individuals. Detectives and investigators are increasingly relying on advanced techniques to uncover these schemes, scrutinizing online activity for red flags. By tracking the digital footprints of perpetrators, investigators can expose fraudulent accounts, pinpoint victims, and stop further harm.
- Cybersecurity experts play a crucial role in this fight by developing innovative strategies to combat online fraud. They work tirelessly to warn the public about common scams and encourage responsible social media use.
- Data analytics is also being utilized to identify patterns and anomalies in online behavior, aiding law enforcement in their efforts to disrupt fraudulent activities.
By means of collaborative efforts between law enforcement, technology companies, and individuals, we can create a safer and more secure online environment for everyone.
Safeguard Your Digital Assets: Hire an Ethical Hacker
In today's interconnected world, safeguarding your digital possessions is paramount. With cyber threats constantly evolving, it's crucial to implement robust security measures. Hiring an ethical hacker can provide a comprehensive assessment of your vulnerabilities and offer tailored recommendations to fortify your defenses. These skilled professionals utilize their expertise to uncover potential weaknesses before malicious actors can exploit them, ensuring the integrity of your valuable data.
A qualified ethical hacker will conduct a intrusive analysis of your network infrastructure, applications, and systems, simulating real-world attacks to expose vulnerabilities. Based on their findings, they'll develop a customized action plan that includes implementing security hardening, training employees on best practices, and establishing incident response protocols. By proactively addressing potential threats, you can minimize the risk of data breaches, financial losses, and reputational damage.
Phone Snooping Exposed
In today's digital age, the lines between privacy and security blur. While mobile monitoring tools can offer a sense of safety, their use often raises ethical questions. Secret phone snooping monitor a someone's activities without their consent. This can range from viewing text messages and call logs to tracking GPS data and even recording audio.
The pros of these tools often outweigh the risks for some users. Individuals may utilize them to protect themselves from potential threats. However, the lack of transparency and potential for abuse make it crucial to view mobile monitoring with care.
- Remember that using these tools without consent can have serious legal consequences
- Always value the privacy of others.
- Employ these tools ethically and thoughtfully.
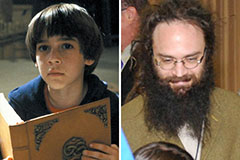 Barret Oliver Then & Now!
Barret Oliver Then & Now! Bug Hall Then & Now!
Bug Hall Then & Now! Kenan Thompson Then & Now!
Kenan Thompson Then & Now! Elin Nordegren Then & Now!
Elin Nordegren Then & Now! Kane Then & Now!
Kane Then & Now!